The Best Crypto Wallets 2024 – Everything About Digital Wallets
Just like with fiat currencies, you also need a wallet for cryptocurrencies. However, a conventional wallet won't get you far, which is why you require a digital alternative. This digital alternative is known as a wallet. Crypto wallets can have the following functions:
The specific functions available depend on the respective wallet. The basic functions include storage, receipt, and sending of cryptocurrencies. However, just because a crypto wallet offers many functions doesn't necessarily mean it's automatically the best choice. There are various types of wallets, each with its advantages and disadvantages.

Table of Contents
- Types of Crypto Wallets
- Cold Wallets
- Hot Wallets
- Exchange Wallets
- Paper Wallets
- The Best Crypto Hardware Wallets 2024
- The Best Desktop Wallets 2024
- The Best Crypto Wallets for Android and iOS 2024
- The Best Exchange Wallets 2024
- What is the Seed Phrase?
- Setting Up Crypto Wallets
- Custodial Wallets vs. Non-Custodial Wallets
- Security Measures for Crypto Wallets - Applicable to All Types
- The Key Criteria for Choosing a Wallet
- Conclusion: The Best Crypto Wallet Depends on Your Personal Requirements
- FAQ about the Best Crypto Wallets
Types of Crypto Wallets
Before you choose a specific wallet, you should be aware of the various types of crypto wallets. In general, there are the following types of wallets to distinguish:
- Cold Wallets
- Hot Wallets
- Exchange Wallets
- Paper Wallets
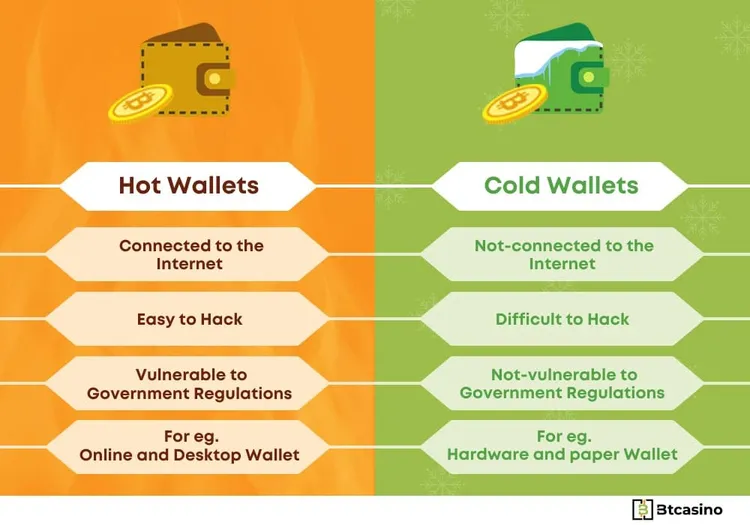
Cold wallets, exchange wallets, and paper wallets do not require further subdivision. However, with hot wallets, we will need to delve into various subtypes. Before we take a closer look at the different types, let's conduct a brief comparison.
| Criteria | Cold Wallets | Hot Wallets | Exchange Wallets | Paper Wallets |
|---|---|---|---|---|
| User-Friendliness | Low | High | Very High | Very Low |
| Required Tech Skills | High | Moderate | Low | Moderate |
| Internet Connection | Offline | Online | Online | Offline |
| Long-term Storage | Suitable | Not Suitable | Not Suitable | Suitable |
| Costs (Acquisition) | Costs | Mostly Free | Mostly Free | Free |
| Privacy | High | Moderate | Low | High |
| Security | Very High | Moderate | Moderate | High |
| Daily Use | Not Suitable | Suitable | Suitable | Not Suitable |
Cold Wallets
Cold Wallets, also known as hardware wallets, are physical devices that are not connected to the internet, providing protection against cyberattacks. They are currently the safest way to store cryptocurrencies. Unlike exchange and hot wallets, they are more suitable for long-term storage rather than daily use.
Just like with other crypto wallets, it is essential to securely store your seed phrase for cold wallets. Otherwise, there is a risk of losing or having all stored cryptocurrencies stolen. Some of the most well-known cold wallets include Ellipal, Ledger, and Trezor. They support nearly all cryptocurrencies on the market.
Hot Wallets
Hot wallets are permanently connected to the internet, making them more susceptible to cyberattacks than hardware wallets or paper wallets. However, they offer a high level of convenience and are accessible at all times. As a result, hot wallets are suitable for those who regularly trade cryptocurrencies. There are various types of hot wallets that can be conveniently downloaded over the internet, often for free. Some hot wallets are designed for specific cryptocurrencies, but most are multi-wallets that support a variety of coins. Modern hot wallets can be connected to exchanges like Uniswap to facilitate quick cryptocurrency exchanges. Some popular hot wallets include Coinbase Wallet, Exodus Wallet, Jaxx Liberty, MetaMask, and Trust Wallet.
Desktop Wallets
Desktop wallets are software applications installed on laptops or PCs. While they are considered hot wallets, they are not connected to the internet, providing an additional layer of protection against cyberattacks. Most desktop wallets are compatible with common operating systems such as Linux, macOS, and Windows. Desktop wallets are safest for Linux or macOS as these operating systems are less susceptible to malware. This is mainly because most people use Windows, leading to more malware targeting that operating system. Well-known desktop wallets include Armory, Atomic Wallet, Electrum, Exodus, and MultiBit.
Mobile Wallets
If you're looking for the best crypto wallet app, you should explore mobile wallets. Mobile wallets are installed on mobile devices like smartphones or tablets. They offer a high degree of flexibility but are typically always connected to the internet. Therefore, they are among the riskier crypto wallets on the market, similar to web wallets. Mobile wallets allow the use of QR codes to connect to exchanges or utilize smart contracts, which is convenient but comes with security risks. Essentially, connecting to a fake QR code can result in the loss of all cryptocurrencies in your mobile wallet. Most mobile wallets are compatible with both Android and iOS. The two most popular mobile wallets are MetaMask and Trust Wallet.
Web Wallets
Web wallets, also known as browser wallets, are accessed through a web browser. They offer the advantage of being accessible from any device without needing to enter your seed phrase. You log in using a username and password, and many web wallets also offer additional security features like two-factor authentication. Since web wallets are hosted by third parties, it's essential to stick with reputable companies to avoid falling victim to scams. An example of a web wallet is Guarda.
Exchange Wallets
Von allen Wallets bieten Exchange Wallets mit Abstand die größte Benutzerfreundlichkeit. Wie aus dem Namen hervorgeht, gibt es Exchange Wallets auf Krypto Börsen wie Binance, Bitpanda, Kraken, KuCoin und OKX. Da sie eine Vielzahl von Handelsfunktionen umfassen, eignen sie sich gut für den täglichen Gebrauch. Der einzige Haken ist, dass Du bei Exchange Wallets nicht die Kontrolle über Deine Coins hast. An dieser Stelle gilt es das beliebte Sprichwort „not your keys, not your coins“ zu nennen.
Es bezieht sich darauf, dass Du bei Exchange Wallets nicht die privaten Schlüssel verwahrst. Stattdessen werden Deine Kryptowährungen von der jeweiligen Krypto Börse kontrolliert. Das geht mit einem hohen Sicherheitsrisiko einher, da selbst die vertrauenswürdigsten Börsen anfällig für Cyberattacken sind. Zudem kannst Du Dir nie zu 100 % sicher sein, dass der Anbieter wirklich seriös ist. In der Vergangenheit gab es immer wieder Fälle, in denen Krypto Börsen unerwartet von der Bildfläche verschwanden und Anleger ihr ganzes Geld verloren.
Paper Wallets
While paper wallets are technically a type of cold wallet, we would like to separate them from hardware wallets since cold wallets are usually associated with hardware devices. The concept behind a paper wallet is straightforward. You generate a public address and a private key online, with the private key designed to be resistant to brute force attacks. You then write down both on a piece of paper and store it securely. If you ever need to access your cryptocurrencies, you can authenticate yourself using the data written on the paper. The drawback of paper wallets is that the paper can be easily damaged or lost.
The Best Crypto Hardware Wallets 2024
| Criteria | Blockstream Jade | Ellipal Titan | Ledger Nano X | Trezor Model T | Trezor Model One | SafePal S1 |
|---|---|---|---|---|---|---|
| Battery-Powered | No | Yes | No | No | No | Yes |
| Display | Yes | Yes | Yes | Yes | Yes | Yes |
| Compatibility | Linux, macOS, Windows | Android, macOS, Linux, Windows | Linux, macOS, Windows | Linux, macOS, Windows | Linux, macOS, Windows | Android, iOS, Windows |
| Price | Starting from 65 Euro | Starting from 170 Euro | Starting from 150 Euro | Starting from 215 Euro | From 65 Euro | Starting from 50 Euro |
| Touchscreen | No | Yes | No | Yes | No | Yes |
| Connectivity | USB, QR-Code | USB, QR-Code | Bluetooth, USB | Micro-USB, USB | USB, QR code | Bluetooth, USB, QR-Code |
| Supported Currencies | Bitcoin, Liquid Sidechain | More than 7,000 | More than 1,500 | More than 1,200 | More than 1.250 | More than 1,000 |
| Additional Features | Multisignature | Self-Destruct Mechanism | App Integration | Password Manager | Multisignature, Password manager | Crypto Exchange Integration |
The Best Desktop Wallets 2024
| Criteria | Armory | Atomic Wallet | Electrum | Exodus | MultiBit |
|---|---|---|---|---|---|
| User-Friendliness | Moderate | High | Moderate | High | High |
| Compatibility | Linux, macOS, Windows | Android, iOS, Linux, macOS, Windows | Linux, macOS, Windows | Android, iOS, Linux, macOS, Windows | Linux, macOS, Windows |
| Configurable | Yes | No | Yes | No | No |
| Crypto Exchange Integration | No | No | No | Yes | No |
| Mobile Version | No | Yes | No | Yes | No |
| Multisignature | Yes | No | Yes | No | No |
| Additional Features | Cold Storage | Staking | Lightning | Crypto Exchange Integration | - |
The Best Crypto Wallets for Android and iOS 2024
| Criteria | Coinbase Wallet | Exodus Wallet | Jaxx Liberty | MetaMask | Trust Wallet |
|---|---|---|---|---|---|
| User-Friendliness | High | High | High | Moderate | High |
| Decentralization | Moderate | Moderate | Low | High | High |
| In-App Purchases | Not possible | Possible | Possible | Not possible | Not possible |
| Crypto Exchange Integration | Yes | Yes | No | No | No |
| Multisignature | No | Yes | No | Yes | Yes |
| Smart Contracts | No | Yes | Yes | Yes | Yes |
The Best Exchange Wallets 2024
| Criteria | Binance | Bitpanda | Kraken | Kucoin | OKX |
|---|---|---|---|---|---|
| Futures | Yes | Yes | Yes | Yes | Yes |
| Live Chat Support | Yes | No | Yes | Yes | No |
| Margin Trading | Yes | Yes | Yes | Yes | Yes |
| Mobile App | Yes | Yes | Yes | Yes | Yes |
| User Count | Over 150 million | Over 4 million | Over 5 million | Over 29 million | Over 50 million |
| Founded Year | 2017 | 2014 | 2011 | 2017 | 2017 |
| Location | - | Vienna, Austria | San Francisco, USA | Mahe, Seychelles | Victoria, Seychelles |
| Staking | Yes | Yes | Yes | Yes | Yes |
| Supported Cryptocurrencies | More than 500 | More than 300 | More than 220 | More than 750 | More than 350 |
What is the Seed Phrase?
When searching for the best crypto wallet, you can't avoid the Seed Phrase. But what exactly is it? The Seed Phrase is nothing more than a security measure that allows you to restore your wallet at any time. It doesn't really matter what type of wallet you have. If you have the Seed Phrase, you can lose the associated hardware or software and still have access to your cryptocurrencies. A Seed Phrase consists of 12 to 24 random words. Since the Seed Phrase is crucial, here are some security measures you should take:
- Safely store your Seed Phrase.
- Ideally, generate the Seed Phrase for your wallet offline.
- Double-check that you've recorded the correct Seed Phrase.
- Never store your Seed Phrase online.
- Under no circumstances should you share your Seed Phrase with others.
If your Seed Phrase falls into the wrong hands, cybercriminals can access all the cryptocurrencies and NFTs in your wallet. Therefore, you must not share it with anyone. There are cases of social engineering on the internet where cybercriminals attempt to extract your Seed Phrase. Don't be fooled under any circumstances. Even a Cold Wallet like Ledger Nano X can be compromised if the recovery phrase is stolen.
Setting Up Crypto Wallets
Before you can use a wallet, you'll need to set it up, and the steps may vary depending on the wallet type. Always refer to the manufacturer's official instructions for your specific model. Here, we provide step-by-step guides for setting up different types of wallets.
Setting Up a Cold Wallet (Hardware Wallet)
A hardware wallet is secure, but it requires careful setup to avoid mistakes or potential risks. Here are the steps:
- Purchase your hardware wallet from a trusted manufacturer like Ledger or Trezor.
- After delivery, check for any signs of damage or tampering.
- Connect your wallet to a secure computer.
- Follow the setup instructions displayed on the device.
- Create a Seed Phrase.
- Set a PIN.
- Safely store your PIN and Seed Phrase.
- Transfer cryptocurrencies from other wallets to your cold wallet.
- Disconnect the hardware wallet from your computer.
- Confirm that the cold wallet functions as intended.
Remember that even on a hardware wallet, your cryptocurrencies are not 100% secure; your behavior plays a crucial role. Risks like using the cold wallet on an infected computer or sharing your Seed Phrase still exist.
Setting Up a Hot Wallet
Setting up a hot wallet is relatively straightforward, but it's essential to avoid accidentally downloading unofficial software from the wrong websites. Follow these steps:
- Choose a specific type of hot wallet.
- Visit the official website of the wallet provider.
- Download the software for your operating system.
- Install the software.
- Launch the software and follow the on-screen instructions.
- Set a password, PIN, and Seed Phrase.
- Securely store all your data.
- Generate a receiving address.
- Receive cryptocurrencies on the correct network.
- Regularly update your wallet.
Just like other software, it's crucial to keep your hot wallets up to date to prevent security vulnerabilities that cybercriminals could exploit.
Setting Up an Exchange Wallet
Unlike cold and hot wallets, you don't really set up exchange wallets. To use exchange wallets, you only need to sign up on a cryptocurrency exchange. Here are the steps:
- Pick a trustworthy cryptocurrency exchange.
- Visit the official website of the exchange.
- Begin the registration process.
- Provide all required information and create an account on the exchange.
- Complete the Know Your Customer (KYC) verification for added security.
- Activate two-factor authentication (2FA) for enhanced security.
After completing these steps, you can access your exchange wallet. However, it's advisable to complete as many KYC verification steps as possible before using the exchange to trade without significant limitations.
Setting Up a Paper Wallet
Setting up a paper wallet is relatively simple, but many people are unsure how the process works. Here's how to set up a paper wallet:
- Ensure your computer is free from malware.
- Visit a trusted website to generate your Seed Phrase.
- Disconnect your computer from the internet.
- Generate the Seed Phrase.
- Visit a reputable paper wallet website.
- Disconnect your computer from the internet again.
- Enter the generated Seed Phrase.
- Create a printable version of your paper wallet.
- Print the paper wallet.
- Store the paper securely.
As you've noticed, you'll need to disconnect your internet connection multiple times during the setup process. This is a necessary security precaution to minimize the risk of compromising your paper wallet during creation. Once you have created your paper wallet, remember to keep it safe. Paper is vulnerable to environmental factors, so consider creating multiple copies to prevent the loss of your cryptocurrencies due to water damage or other accidents.
Custodial Wallets vs. Non-Custodial Wallets
In your search for the best crypto wallets, you'll come across Custodial Wallets and Non-Custodial Wallets. The main difference between these two types of wallets lies in the level of control you have over your private keys.
- Custodial Wallets (Centralized Wallets):
- Custodial wallets are managed by third parties, often cryptocurrency exchanges or wallet service providers.
- With custodial wallets, you don't have direct control over your private keys; the service provider holds and manages them on your behalf.
- These wallets are known for their convenience, as they typically provide user-friendly interfaces and integrated exchange services.
- Users of custodial wallets typically need to complete a verification process.
- The security of your funds relies on the trustworthiness of the service provider. If the provider gets hacked or experiences issues, your funds may be at risk.
- Non-Custodial Wallets (Decentralized Wallets):
- Non-custodial wallets give you full control over your private keys. You generate and manage your keys independently.
- They are considered more secure because you are the sole custodian of your cryptocurrencies.
- If you use a hardware wallet, your coins are stored offline, adding an extra layer of security.
- You do not need to go through a verification process to use non-custodial wallets.
- Many non-custodial wallets offer anonymity, allowing you to use them without revealing personal information.
In summary, non-custodial wallets are generally considered safer because you have complete control over your crypto assets and private keys. However, custodial wallets offer convenience and are often used for trading and quick access to funds. The choice between the two depends on your priorities: security or convenience. It's also common for crypto users to use both types of wallets based on their specific needs.
Security Measures for Crypto Wallets - Applicable to All Types
Securely managing a crypto wallet doesn't have to be complicated. There are essential rules that apply to all types of wallets. By following these security measures, you can significantly reduce the risk of your cryptocurrencies falling into the wrong hands or being lost.
1. Create Backups
Losing your seed phrase can be frustrating. Many people have lost access to their wallets in the past, resulting in the loss of valuable cryptocurrencies. Create backups of your seed phrase, but ensure that you store them securely.
2. Never Enter Sensitive Data on Phishing Sites
Cybercriminals often create phishing websites to steal sensitive data. When downloading a wallet, always verify the website's authenticity. Using a fake website can lead to the loss of all your cryptocurrencies.
3. Beware of Social Engineering
Social engineering is as dangerous as phishing. It involves manipulation to gain your trust, leading to the extraction of crucial information like your seed phrase. Always remain cautious, even when dealing with people you've known for a while. In the world of cryptocurrencies, high vigilance is crucial.
4. Stay Informed About Legal Changes
Cryptocurrency regulations can change, and these changes may impact how you store your coins. Staying informed about the legal landscape is essential. Some discussions, such as the potential requirement for Ledger to disclose customer seed phrases to financial authorities, have generated controversy. It might never be implemented, but staying informed is key.
5. Use Trustworthy Sources Only
To mitigate the risk of encountering phishing sites, rely exclusively on reputable sources. Avoid downloading wallets or obtaining information from unverified or suspicious sources. Be cautious about where you get your crypto-related information.
6. Check the Security of Your Devices
Even the best wallet won't protect your assets if you install it on a device infected with malware or connect it to an unsafe environment. Ensure the device you use is secure. Conduct thorough antivirus scans, and consider using a fresh operating system for added security.
7. Test Wallet Functionality with Small Test Amounts
After setting up a wallet, it should function correctly. However, occasional issues can arise due to errors. To avoid surprises and ensure your crypto transfers work smoothly, test the wallet's functionality with small test amounts before moving larger sums.
8. Securely Store Your Seed Phrase:
Lastly, but most importantly, always store your seed phrase securely. Regardless of the type of wallet, your seed phrase is the key. While it provides access to your wallet, it can also grant access to others if it falls into the wrong hands. Keep your seed phrase private and secure at all times.
By following these security measures, you can significantly enhance the safety of your cryptocurrency holdings, regardless of the type of wallet you use. Always prioritize security to protect your assets.
The Key Criteria for Choosing a Wallet
Finding the best crypto wallet can be quite the challenge. To make your decision a bit easier, we've compiled the most important criteria for you:
1. User-Friendliness
No wallet should be so complicated that you spend ages figuring out how to perform a specific action. User-friendliness is always a crucial criterion. However, keep in mind that higher user-friendliness might come with lower security. A prime example of this trade-off is found in Exchange Wallets and Hot Wallets, which typically don't match the security level of Hardware Wallets.
2. Features
Some wallets come with integrated features. For instance, with MetaMask or Trust Wallet, you can connect to an exchange and swap your coins for other cryptocurrencies. Additional features are particularly interesting if you're into cryptocurrency trading.
3. Compatibility
Not every wallet is compatible with every device. Therefore, you should check whether the wallet you're interested in can be used on your device. Mobile wallets are usually for smartphones or tablets, but some also offer browser extensions, like MetaMask.
4. Costs
Wallet costs are generally quite reasonable. You won't have to pay for Exchange Wallets, Hot Wallets, or Paper Wallets. The only paid wallets are Cold Wallets or Hardware Wallets. However, you don't necessarily need an expensive device. SafePal S1, for example, starts at just €50, and Blockstream Jade is only around €65.
5. Security
Security is, undoubtedly, the most critical criterion for us. Despite high user-friendliness, we advise against long-term storage in Exchange Wallets or Hot Wallets. If you truly want to be secure, you should keep only a small portion of your cryptocurrencies in Exchange Wallets and Hot Wallets. This way, you can quickly swap your coins, play in a crypto casino, or execute trades when required. The majority of your cryptocurrencies should reside in a Cold Wallet to protect your assets from cyberattacks.
6. Supported Cryptocurrencies
Most older wallets were only compatible with a single cryptocurrency. In the past, it was common to have separate wallets for Bitcoin, Ethereum, Litecoin, and other coins. While that's no longer the case, the supported cryptocurrencies can still vary from one wallet to another. Therefore, always check whether the wallet you're considering works with your preferred cryptocurrencies.
Conclusion: The Best Crypto Wallet Depends on Your Personal Requirements
Determining the best crypto wallet can be challenging due to the various selection criteria. Ultimately, the best wallet choice depends on your personal needs. If you plan to use your wallet daily, Exchange Wallets or Hot Wallets are a good choice. However, for long-term storage, Cold Wallets like Hardware Wallets and Paper Wallets are the safer option. It's actually a great idea to use multiple types of wallets for different purposes. This approach allows you to cover various use cases effectively and provides additional security.
FAQ about the Best Crypto Wallets
Whether you're looking for the best crypto hardware wallet or the best crypto wallet app, it ultimately depends on your personal requirements. In some cases, a hot wallet might be the right choice. Alternatively, you can use multiple types of wallets for different purposes. If secure storage is your top priority, we recommend Ledger Nano X.
Even if you opt for a hardware wallet, your cryptocurrencies are not automatically protected from theft. Therefore, you should always take some precautions. This includes securely storing your seed phrase and never sharing it under any circumstances. Furthermore, you should never connect your wallets to devices infected with malware.
Exchange wallets offer useful features and a high level of convenience. The only issue is that you do not have control over the private keys to your wallet. Instead, the keys are held by the respective cryptocurrency exchange, which comes with an additional risk. Even with a reputable provider, it's theoretically possible to lose your cryptocurrencies.
The setup process depends not only on the type of wallet but also on the specific model. If you're unsure, you can refer to our step-by-step guides. If that's not sufficient, it's best to follow the manufacturer's instructions.




